High-profile individuals and their families face risks shaped by their visibility, wealth, and influence.
Threats range from traditional kidnapping and extortion to more sophisticated tactics like cyber-enabled blackmail and virtual abductions. While physical abductions attract most media attention, these alternative methods are growing in prevalence and complexity.
This article explores those threats using the ongoing Nancy Guthrie case as a primary example, and outlines proven prevention strategies employed by security and executive protection firms.
Don’t have time to read? Watch, or listen 👇
Table of Contents
The Threat Landscape: Kidnapping, Blackmail, and the Case That Changed the Conversation

Kidnapping remains one of the most direct and feared threats facing high-profile individuals and their families. When family members are targeted, perpetrators leverage emotional distress to escalate ransom demands, sometimes into the millions. Blackmail, by contrast, relies on compromising information obtained through hacking, surveillance, or insider leaks to extract payments or compel specific actions. Beyond these, tactics such as extortion schemes, doxing (the public release of private information), and virtual kidnappings, where scammers impersonate abductors without any actual abduction taking place, add further layers of complexity.
Technology has significantly amplified these methods. Dark web forums are used to trade leaked credentials, while AI tools now enable convincing deepfake videos for blackmail purposes. High-profile individuals are particularly exposed during international travel, where unfamiliar environments create additional opportunities for abduction or opportunistic extortion. Financial gain remains the primary motive, though ideological grievances and personal vendettas are increasingly common factors, as seen in targeted harassment campaigns against executives in healthcare and technology.
The abduction of Nancy Guthrie, the 84-year-old mother of NBC Today co-host Savannah Guthrie, offers a stark illustration of these dangers. On January 31, 2026, Nancy was last seen at her home in Tucson, Arizona, after family members dropped her off following dinner. Authorities classified the incident as a kidnapping based on evidence at the scene, including a disconnected doorbell camera at 1:47 a.m. and her pacemaker app going offline shortly afterward. Ransom demands of $6 million followed, with threats made against her life if deadlines were not met.
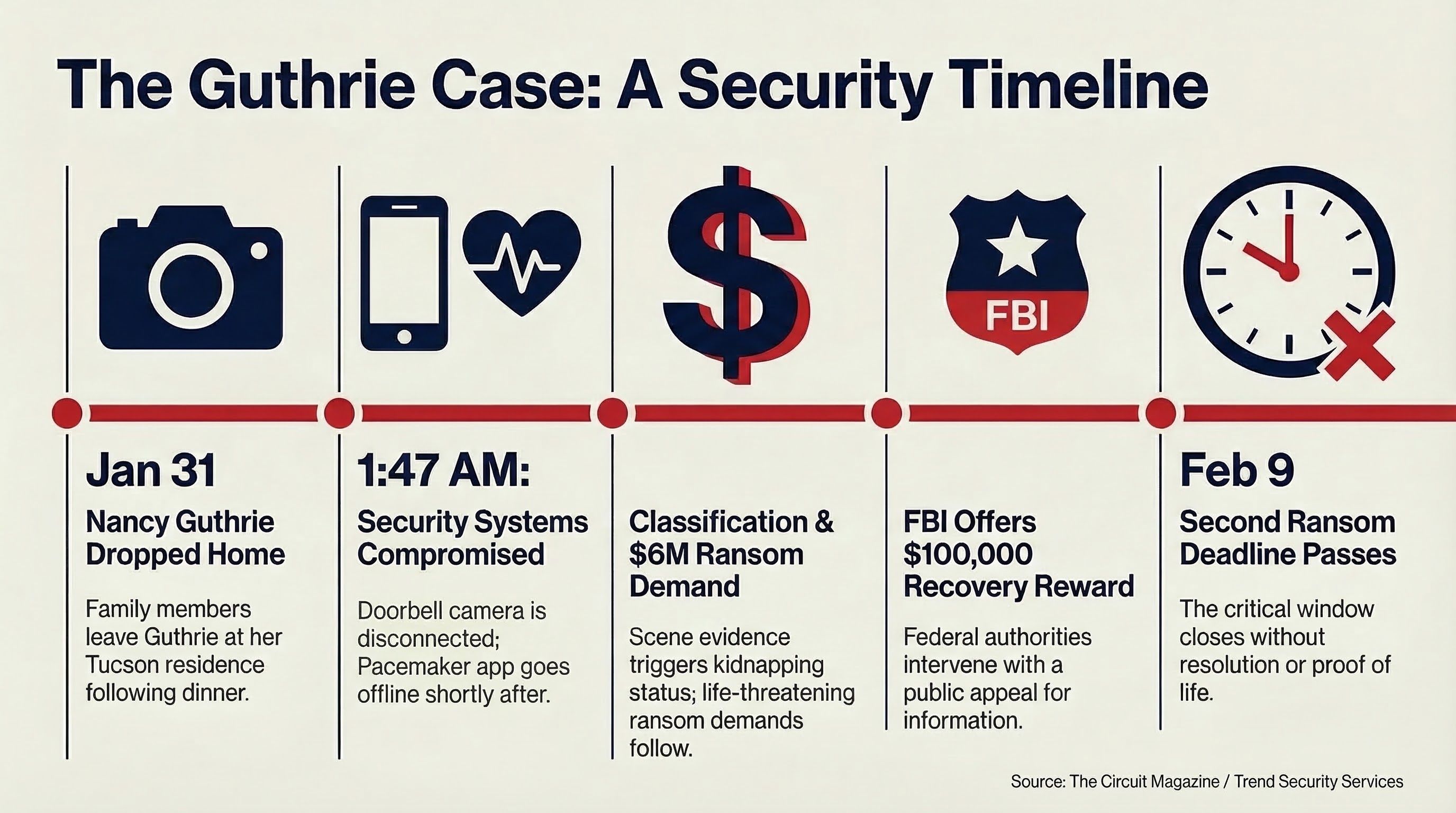
The family publicly appealed for help, with Savannah Guthrie releasing video statements urging the public to assist law enforcement. The FBI offered a $100,000 reward for information leading to Nancy's recovery. As of February 9, 2026, a second ransom deadline had passed without resolution, heightening fears for her safety.
Although this case remains active, it already offers important insights for high-profile individuals, their families, and the security professionals who protect them. The lessons below draw on the case timeline, available evidence, and expert analysis, highlighting gaps that practitioners can learn from and act on.
Extended Family Members as High-Value Targets
The abduction of an elderly parent demonstrates clearly that threats extend beyond the primary high-profile individual. Targeting vulnerable relatives is a deliberate tactic, one that exploits emotional leverage to drive up ransom demands or compel compliance. Security firms should conduct comprehensive risk assessments covering the entire family, including aging relatives who live independently. This means integrating medical alert systems with security monitoring and ensuring all household members receive personal safety training.
Targeting vulnerable relatives is a deliberate tactic, one that exploits emotional leverage to drive up ransom demands or compel compliance.
Skepticism and Verification in Handling Ransom Demands
Multiple ransom communications were sent to media outlets, yet the absence of proof of life caused investigators and analysts to question their legitimacy, particularly as deadlines passed. This raises a real concern about opportunistic actors exploiting high-profile cases for financial gain. High-profile individuals and their security advisors should have kidnap, ransom, and extortion (KR&E) insurance in place, with established protocols requiring proof of life before any negotiation begins. Threat monitoring programs that scan social media and the dark web in real time help distinguish genuine demands from copycat schemes quickly.
Lead Pursuit and False Positives
The swift detention and subsequent release of a person of interest illustrates both the urgency of time-sensitive investigations and the risk of misdirection. In this instance, the individual's possible connection as a delivery driver shows how routine daily interactions can generate false leads. Pre-incident due diligence, including logging all visitors, deliveries, and service personnel with photo verification, is a practical mitigation measure. Post-incident, protective intelligence and overwatch programs can cross-reference leads and reduce false positives. This case also highlights the value of cross-agency collaboration, something high-profile families can facilitate through retained legal and security consultants.

Media Management
The Guthrie family's public video appeals have amplified awareness of the case and the FBI reward offer. However, media visibility also creates exposure to exploitation. Developing a media strategy in advance is essential: designating spokespeople, controlling the narrative, and avoiding any disclosure that reveals operational vulnerabilities. Security firms can support this with real-time digital threat monitoring to detect emerging risks such as doxing or coordinated harassment. Privacy tools, including address obfuscation and encrypted communications, further limit the public exposure that can inspire copycat activity.
The detention of a person of interest near the U.S.-Mexico border suggests potential international elements, which is not uncommon in ransom-motivated kidnappings. High-profile individuals with properties in border regions, or who travel through them regularly, should incorporate geopolitical intelligence into their threat assessments. Secure transportation plans, including armored vehicles where appropriate, and advance route scouting are standard practice. Established security firms maintain global networks capable of rapid extraction and are practiced in countering the predictable routines that create opportunities for adversaries.

Leveraging Technology for Timelines and Evidence
Data from Nancy Guthrie's pacemaker and doorbell camera helped establish a timeline that proved valuable to investigators. However, the fact that both devices were disabled by perpetrators highlights a critical limitation of relying on single-layer technology. Integrating wearable health monitors into a broader security ecosystem, with real-time alerts to security teams, provides an additional layer of protection. Post-incident, this data can significantly accelerate response timelines. Security teams should conduct regular technology audits and cybersecurity reviews to prevent devices from being hacked or disabled.
These lessons reinforce the case for proactive security planning. As the investigation progresses, further insights will emerge. What the case already reveals is how seemingly minor oversights can escalate into serious vulnerabilities. High-profile individuals and their families should work with executive protection firms that specialise in translating these lessons into tailored, practical defenses.
While physical kidnappings like the Guthrie case attract the most media attention, digital blackmail is a growing and often underreported threat. Hackers steal sensitive data from personal devices or corporate networks and threaten to release it unless demands are met.
The rise of virtual kidnappings means perpetrators can extort payments without any actual abduction taking place. The scheme exploits panic, and it works.
Virtual kidnappings represent a related tactic: perpetrators use spoofed calls and AI-generated voices to convince targets that a loved one has been abducted. These schemes exploit panic without any actual abduction occurring and, while low-risk for the perpetrators, can be highly effective. Other tactics include social engineering, where insiders or impersonators gain access to private information for extortion purposes. For high-net-worth individuals (HNWIs) in finance or cryptocurrency, threats increasingly involve the theft of digital assets or doxing to incite public pressure. The rise of extremist online influencers has also contributed to targeted residential harassment, blending digital threats with physical intrusion.
Security and executive protection firms consistently emphasise proactive, multi-layered approaches to managing these risks, combining physical safeguards, threat intelligence, and technology to stay ahead of adversaries.
Residential Security
The homes of high-profile individuals and their families are prime targets, as the Guthrie case illustrates. Leading security firms recommend deploying residential security teams (RSTs) alongside advanced surveillance cameras and access control systems. A thorough residential security assessment is essential to identify vulnerabilities such as weak entry points. AI-powered cameras and drone monitoring provide real-time deterrence and alert RSTs to suspicious activity before incidents escalate.

Threat Monitoring and Intelligence
Threat monitoring is a core component of any executive protection programme. These programmes scan social media, the dark web, and public sources for open-source intelligence (OSINT) relating to the protected individual or their family. The most effective platforms combine experienced intelligence analysts with technology, reporting findings directly to field teams rather than relying on automated tools alone. Watch lists can be configured to detect impersonation attempts and emerging threats in near real time. Protective intelligence also analyses geopolitical conditions and crime patterns in anticipated travel areas, allowing teams to adjust planning in advance. For virtual kidnapping scenarios, verification protocols, such as confirming the alleged victim's location via secure channels, are essential to preventing hasty and unnecessary payments.
The Nancy Guthrie case is a reminder that vulnerability does not always track with prominence. Family members living independently, elderly relatives, those outside the immediate protection bubble, can represent the most exploitable targets in any principal's network. By combining rigorous residential security, proactive threat monitoring, and appropriate financial protections such as KR&E insurance, firms can materially reduce exposure to these threats. Preparation and awareness remain the most reliable tools for turning potential vulnerabilities into defensible positions.
Richard Rempo is a specialist in homeland security and counterterrorism with over 25 years of experience across federal and state law enforcement and private-sector security leadership.
As Chief Operating Officer of Trend Security Services, Richard oversees security planning, risk and threat assessments, and continuous threat monitoring for high-profile clients worldwide.
This article was published by The Circuit Magazine. For weekly intelligence briefings on the security and protection industry, subscribe to On The Circuit.

